ISARA Insights Blog
Featured Blog Post
10 Reasons Why Cryptographic Management is Critical
Sinisha Patkovic
Oct 20, 2021
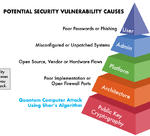
Why is cryptography suddenly becoming such a big topic? Let’s face it. Cryptography has been at the core of every secure transaction since the dawn of the Internet — unassuming and low profile, it has been working its security magic all the way from hardware to apps. Public key cryptography, to be more exact, ensures the authentication and identity of all transactions and participants in the digital world.

Tags:
10 Reasons Why Cryptographic Management is Critical
Sinisha Patkovic
Oct 20, 2021
Why is cryptography suddenly becoming such a big topic? Let’s face it. Cryptography has been at the core of every secure transaction since the dawn of the Internet — unassuming and low profile, it has…

Myth-Busting the Quantum Threat: The Top 3 Misconceptions About Quantum-Safe Migrations
Paul Lucier
Jul 23, 2019
Part of our mission at ISARA is to educate and raise awareness of the security risks introduced by large-scale quantum computing. Since I joined ISARA in 2016, I’ve spoken to individuals, enterprises,…

How Quantum Computing’s Threat to Security is Different from All Other Security Breaches
Mike Brown
Jan 11, 2018
The quantum threat represents the first time in history that a cybersecurity breach will be the result of a complete break of modern public-key cryptography. For many, this information might come as a…
The Quantum-Safe Migration: Cryptography’s Overhaul
Scott Totzke
Oct 26, 2017
On October 17th, the Hudson Institute – a think tank headquartered in Washington, DC – gathered quantum computing and cybersecurity experts to explore the quantum threat from a security and policy perspective.…

Do You Know About Quantum’s Threat to OTA Software Updates?
Alex Truskovsky
Oct 17, 2017
Today, remotely updating a device’s software - such as a connected car or smartphone - is easy and cost-effective. There’s no need to physically return the device to the manufacturer, which happily saves…
