ISARA Insights Blog
Tags:
The Peggy Smedley Show: Quantum Threats and Benefits
ISARA Corporation
Apr 26, 2018
On April 24, ISARA Corporation's VP of Business Development, Paul Lucier, was invited to join The Peggy Smedley Show - one of the most influential, Internet of Things (IoT) podcasts discussing relevant…

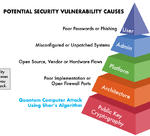
How Quantum Computing’s Threat to Security is Different from All Other Security Breaches
Mike Brown
Jan 11, 2018
The quantum threat represents the first time in history that a cybersecurity breach will be the result of a complete break of modern public-key cryptography. For many, this information might come as a…
Quantum Computing: Its Emergence & Implications on Information Security
Mark Pecen
Dec 19, 2017
Leading governments around the globe, along with major corporations, including IBM, Google, Microsoft, have all made substantial investments in the development of large-scale quantum computers, just in…

Next-Generation Cryptographic Certificates: Toward Quantum-Safe Identity
Mark Pecen
Nov 08, 2017
Cryptographic certificates are used to prove a person’s, system’s, company’s or other entity’s identity. Today, cryptographic certificates are based on public-key cryptography, which is vulnerable to quantum…

The Quantum-Safe Migration: Cryptography’s Overhaul
Scott Totzke
Oct 26, 2017
On October 17th, the Hudson Institute – a think tank headquartered in Washington, DC – gathered quantum computing and cybersecurity experts to explore the quantum threat from a security and policy perspective.…
