ISARA Insights Blog
Featured Blog Post
How Quantum Computing’s Threat to Security is Different from All Other Security Breaches
Mike Brown
Jan 11, 2018
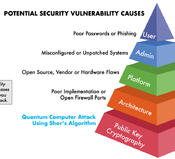
The quantum threat represents the first time in history that a cybersecurity breach will be the result of a complete break of modern public-key cryptography. For many, this information might come as a surprise. There seems to be a new security breach almost every day; in January 2018 a bug was discovered in Intel’s chips affecting most computers, and since then several other significant breaches and alarming cybersecurity statistics were announced. Yet modern public-key cryptography such as RSA and elliptic-curve cryptography (ECC) - the very foundation of cybersecurity - haven’t been broken via an efficient attack on commercialized products when implemented correctly.
Tags:
How Quantum Computing’s Threat to Security is Different from All Other Security Breaches
Mike Brown
Jan 11, 2018
The quantum threat represents the first time in history that a cybersecurity breach will be the result of a complete break of modern public-key cryptography. For many, this information might come as a…
Quantum Computing: Its Emergence & Implications on Information Security
Mark Pecen
Dec 19, 2017
Leading governments around the globe, along with major corporations, including IBM, Google, Microsoft, have all made substantial investments in the development of large-scale quantum computers, just in…

Next-Generation Cryptographic Certificates: Toward Quantum-Safe Identity
Mark Pecen
Nov 08, 2017
Cryptographic certificates are used to prove a person’s, system’s, company’s or other entity’s identity. Today, cryptographic certificates are based on public-key cryptography, which is vulnerable to quantum…

How Quantum Computing Increases Cybersecurity Risks
Scott Totzke
May 23, 2017
The following is an excerpt from a contributed opinion piece on CSO by Scott Totzke, CEO & Co-Founder of ISARA Corporation. Imagine you wake up one morning, assuming everything is as you left it the…
